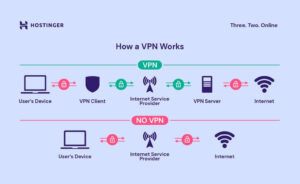
In the world of Virtual Private Networks (VPNs), the protocol you choose can significantly impact your online security, speed, and overall experience. VPN protocols dictate how your data is transmitted over the internet, influencing everything from encryption to connection stability. In this article, we’ll break down the most common VPN protocols—OpenVPN, L2TP, IKEv2, and others—so you can make an informed choice for your online needs.
What Are VPN Protocols?
VPN protocols are sets of rules that determine how data is transmitted between your device and the VPN server. Each protocol has its own strengths and weaknesses in terms of security, speed, and ease of use. Understanding these differences is crucial for selecting the right VPN service for your specific requirements.

1. OpenVPN
Overview
OpenVPN is one of the most popular and versatile VPN protocols available today. It is open-source, which means its code is publicly available for scrutiny and improvement.
Strengths
- High Security: Uses AES-256 encryption, making it extremely secure.
- Customizable: Offers a range of configuration options, allowing users to tailor it to their needs.
- Cross-Platform Support: Compatible with various operating systems, including Windows, macOS, Linux, Android, and iOS.
Weaknesses
- Complex Setup: May require some technical knowledge to configure properly.
- Speed Variability: Performance can vary depending on server load and distance.
2. L2TP/IPsec (Layer 2 Tunneling Protocol)
Overview
L2TP is often paired with IPsec for encryption, providing a secure connection. This combination is commonly used in corporate environments.
Strengths
- Good Security: Offers strong encryption through IPsec.
- Widely Supported: Natively supported by most operating systems, making it easy to set up.
Weaknesses
- Speed Issues: Typically slower than other protocols due to double encapsulation (L2TP and IPsec).
- Firewall Issues: May face issues with firewalls and NAT (Network Address Translation) due to the use of multiple ports.
3. IKEv2/IPsec (Internet Key Exchange version 2)
Overview
IKEv2 is a tunneling protocol that is often combined with IPsec for encryption. It is known for its speed and stability, especially on mobile devices.
Strengths
- Fast Connection: Offers quick reconnection times, making it ideal for mobile users who switch networks frequently.
- Strong Security: Provides robust encryption through IPsec.
- Stability: Maintains a stable connection, even when switching between Wi-Fi and mobile data.
Weaknesses
- Limited Compatibility: Not as widely supported on all platforms as OpenVPN.
- Less Flexible: Fewer configuration options compared to OpenVPN.
4. PPTP (Point-to-Point Tunneling Protocol)
Overview
PPTP is one of the oldest VPN protocols and was developed by Microsoft. While it is fast and easy to set up, its security features are outdated.
Strengths
- Easy Setup: Simple to configure, making it user-friendly.
- High Speed: Offers fast connection speeds due to minimal encryption.
Weaknesses
- Low Security: Vulnerable to various security threats, making it unsuitable for sensitive data.
- Limited Encryption: Uses weak encryption methods, which can be easily compromised.
5. SSTP (Secure Socket Tunneling Protocol)
Overview
SSTP is a Microsoft-developed VPN protocol that uses SSL/TLS for encryption. It is particularly effective for bypassing firewalls.
Strengths
- Strong Security: Provides robust encryption through SSL/TLS.
- Firewall Bypass: Can easily navigate through firewalls and NAT.
Weaknesses
- Windows-Centric: Primarily designed for Windows, limiting compatibility with other platforms.
- Limited Open Source Options: Not as customizable as OpenVPN.
Choosing the Right VPN Protocol
When selecting a VPN protocol, consider the following factors:
- Security Needs: If security is your top priority, opt for protocols like OpenVPN or IKEv2/IPsec.
- Speed Requirements: For high-speed connections, IKEv2/IPsec or OpenVPN (with the right settings) are preferable.
- Ease of Use: If you want a straightforward setup, L2TP/IPsec or PPTP may be more suitable.
- Compatibility: Ensure the protocol you choose is compatible with your devices and operating systems.
Conclusion
Understanding VPN protocols is essential for making informed decisions about your online security and privacy. Each protocol has its unique features, strengths, and weaknesses. By evaluating your specific needs—whether it’s security, speed, or ease of use—you can choose the right VPN protocol for your digital lifestyle.
Call to Action
Ready to enhance your online security? Explore our top VPN recommendations HERE that support various protocols, ensuring you find the perfect fit for your needs. Protect your privacy today and enjoy a safer internet experience!



Great beat ! I would like to apprentice while you amend your web site, http://www.hairstylesvip.com how could i subscribe for a blog site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear concept
Good web site! I truly love how it is easy on my eyes and the data are well written. http://www.hairstylesvip.com I am wondering how I could be notified whenever a new post has been made. I’ve subscribed to your RSS which must do the trick! Have a nice day!
Thanks for posting. I really enjoyed reading it, especially because it addressed my problem. http://www.hairstylesvip.com It helped me a lot and I hope it will help others too.
Great content! Super high-quality! Keep it up! http://www.ifashionstyles.com
Thanks a lot for being an aware & active reader! We are glad to have you here and more importantly happy to hear this helped! 🙂
I’ve been browsing online greater than three hours lately, yet I never found any attention-grabbing article like yours. It is pretty value sufficient for me. Personally, if all website owners and bloggers made good content as you did, the web will likely be much more useful than ever before.
Thank you for your loving words. We are grateful to hear your experience about the same and more importantly that it serves al collectively. 🙂
Thank you for your articles. They are very helpful to me. May I ask you a question? http://www.kayswell.com
Thank you for the appreciation, we are glad we could support you in the same. Yes, feel free to ask anything you need, we are happy to serve 🙂
It’s a pity you don’t have a donate button! I’d definitely donate to this fantastic blog! I guess for now i’ll settle for bookmarking and adding your RSS feed to my Google account. I look forward to new updates and will share this blog with my Facebook group. Talk soon!
When someone writes an piece of writing he/she keeps the thought of a user in his/her brain that how a user can know it. So that’s why this paragraph is outstdanding.
We’re a group of volunteers and starting a new scheme in our community. Your website offered us with helpful information to work on. You’ve done a formidable task and our whole community will be thankful to you.
In this grand design of things you actually secure an A+ with regard to effort and hard work. Where you lost us was first on all the details. You know, people say, the devil is in the details… And that couldn’t be more correct right here. Having said that, allow me reveal to you just what did work. Your article (parts of it) is actually incredibly engaging and this is most likely why I am taking the effort in order to comment. I do not really make it a regular habit of doing that. Next, even though I can easily notice a jumps in reasoning you come up with, I am not necessarily certain of just how you appear to unite your points which inturn make your final result. For now I will, no doubt yield to your issue however wish in the foreseeable future you actually connect the facts much better.
This is my first time visit at here and i am actually happy to read everthing at alone place.
I am regular reader, how are you everybody? This post posted at this web page is genuinely pleasant. http://www.kayswell.com
When I initially commented I clicked the “Notify me when new comments are added” checkbox and now each time a comment is added I get several emails with the same comment. Is there any way you can remove people from that service? Many thanks! http://www.kayswell.com
Ahaa, its fastidious discussion on the topic of this article at this place at this website, I have read all that, so now me also commenting at this place.
Hello very nice web site!! Man .. Beautiful .. Amazing .. I will bookmark your site and take the feeds also? I am satisfied to seek out so many useful information here in the put up, we want work out extra techniques on this regard, thank you for sharing.
I don’t even know how I ended up here, but I thought this post was great. I do not know who you are but definitely you’re going to a famous blogger if you are not already 😉 Cheers! http://www.ifashionstyles.com
Great blog you’ve got here.. It’s difficult to find excellent writing like yours these days. I seriously appreciate individuals like you! Take care!! http://www.kayswell.com
Hi to every body, it’s my first pay a visit of this weblog; this weblog contains remarkable and genuinely excellent material designed for readers. http://www.ifashionstyles.com
Attractive section of content. I just stumbled upon your web site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Anyway I抣l be subscribing to your augment and even I achievement you access consistently fast.
What’s up, after reading this awesome post i am too happy to share my familiarity here with colleagues.
My partner and I stumbled over here coming from a different page and thought I might check things out. I like what I see so i am just following you. Look forward to finding out about your web page yet again.
Great blog you’ve got here.. It’s difficult to find excellent writing like yours these days. I seriously appreciate individuals like you! Take care!!